
Threat modeling, where your code lives.
Dethereal is a Claude Code plugin that turns anything an LLM can parse about your system — code, IaC, docs, diagrams, command output, even live runtime — into a version-controlled threat model that Dethernety can analyze.
$ claude > /dethereal:threat-model guided 11-step workflow — discover, classify, enrich, publish ✓ scanned 247 files · 18 components found ✓ 24 data flows mapped across 6 trust boundaries ✓ readiness B+ · publishing snapshot to Dethernety → analyzing now · findings will appear in workspace
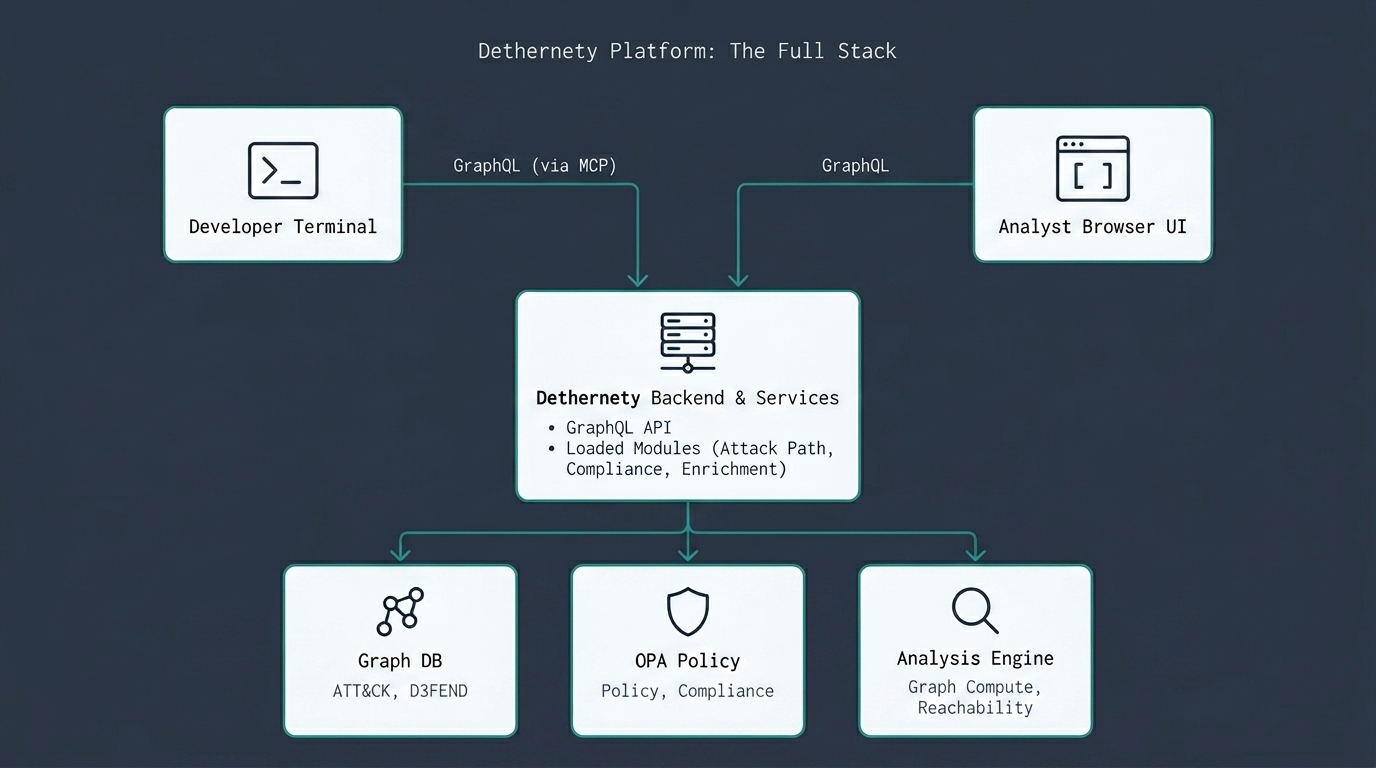
Two interfaces, one backend. Dethereal publishes from the terminal; analysts work from the browser; both share the same model graph.
One command.
Eleven steps you don't type.
/dethereal:threat-model runs a guided eleven-step workflow. Below it's grouped into five stages, with a session break in the middle: the first five steps build the structural model, the last six enrich it with security context. Specialist agents do the legwork at each step; you adjudicate before anything is written to disk.
Plain chat asks you to articulate what you don't yet know. Plain commands ask you to know which one comes next. Staged delegation breaks the artifact into ordered stages, hands each step to a specialist agent, and leaves you the part you're actually good at: recognising whether a proposal is right.
Each role's permissions are enforced at the tool layer rather than in the system prompt — boundaries the agents cannot cross even if a prompt tells them to. Each stage also maps to a standalone slash command, for when you only want to run one.
Read the full essayFour specialists, four scopes.
Each agent runs in a tool sandbox shaped to its job. The orchestrator delegates; the others do one thing each.
Owns the state machine. Presents the scout's discovery to you, writes confirmed elements to disk, drives the workflow forward step by step.
Scans code, IaC, docs, and (with consent) live infrastructure. Produces a discovery report with cited sources and two confidence buckets per component.
The only agent that writes attributes. Two-pass classification against the class library, schema-driven attribute filling, credential topology.
Computes the seven-factor quality score, runs the three readiness gates, and decides whether the model is publish-ready.
- 01
Initialize
/dethereal:createStart from a free-text description, a template, or pull an existing model down from the platform for offline editing. The model is a directory of small JSON files in your repo, committed and diffed like any other code.
~/your-repo> /dethereal:create "React frontend → Go API → Postgres" ⠋ scaffolding model from description… ✓ created threat-model/ (4 components, 1 boundary) → ready for /dethereal:discover
- 02
Discover
/dethereal:discoverA discovery agent reads anything the LLM can parse — code and IaC first (Terraform, Kubernetes manifests, Dockerfiles, OpenAPI specs, CI config), then docs, READMEs, architecture notes, even screenshots of diagrams or vendor consoles. For runtime-only components, paste in the output of kubectl describe or aws describe — or, with explicit consent, let the agent run those commands against live infrastructure. It proposes components, boundaries, and data flows; you confirm what's right.
~/your-repo> /dethereal:discover ⠋ scanning 247 files across 12 paths… ✓ 18 components · 6 trust boundaries · 24 data flows → wrote structure.json, dataflows.json
- 03
Classify & map
/dethereal:classifyAssign classes to components and data items, draw the trust boundaries the discovery pass missed, mark the crown jewels. Each change is a small file edit, reviewable like any other diff.
~/your-repo> /dethereal:classify ✓ 18 / 18 components classified ✓ 12 data items tagged (3 crown jewels) → 0 unclassified elements remaining
- 04
Enrich
/dethereal:enrichPopulate the security attributes the platform needs to compute exposures and attack paths: credentials, monitoring tools, network topology, MITRE ATT&CK coverage. Done as a guided pass, one element at a time.
~/your-repo> /dethereal:enrich ✓ enriched 18 components ✓ MITRE technique coverage: 76% → readiness score: B+ (publish-ready)
- 05
Publish
/dethereal:sync pushCommit the model alongside your code. When you're ready, publish a snapshot to Dethernety; the platform replaces its copy and runs analysis. There is no continuous sync between the two: local is the working copy, publishing is an explicit action.
~/your-repo> /dethereal:sync push ⠋ uploading snapshot… ✓ published as model_8f3a91 · platform analyzing → findings will appear in Dethernety workspace
A threat model that lives in git.
Dethereal produces a directory of small JSON files, one per concern. The diffs read clearly in a pull request. Components become graph nodes; data flows become edges; boundaries define subgraphs. The format maps directly to the platform's graph schema.
- Read it in a pull request like any other change
- Revert to any commit; no platform round-trip
- Publish on your schedule, not on a sync engine's
├── manifest.json ├── structure.json # components, boundaries ├── dataflows.json # edges between components ├── data-items.json # assets, crown jewels └── attributes/ ├── api-gateway.json ├── postgres.json └── auth-service.json
Install the plugin. Type a slash command.
Dethereal lives where your code lives. No separate UI, no new account. Publish to Dethernety only when the model is ready.
Get Started