
Threat analysis, with you in the loop.
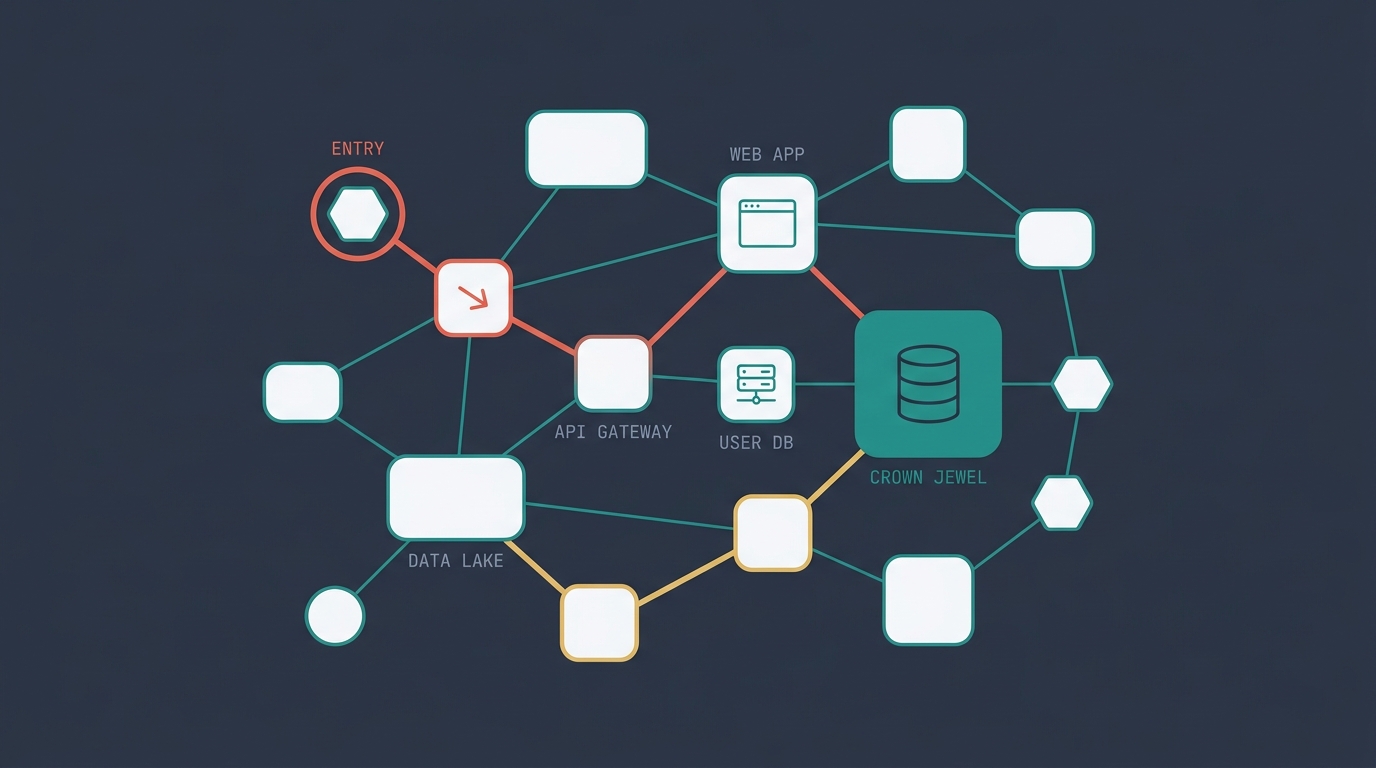
A multi-agent workspace that runs scope-gated analyses on your Dethernety threat models. Findings, attack scenarios, readiness, and exports for every stakeholder — anchored in the same graph.
Plain AI threat analysis runs blanket: agents scan everything, propose anything, hallucinate freely. The Copilot inverts the default — scope is negotiated with you before any analysis runs, agents follow a deterministic plan, and findings carry cited evidence. You stay in the loop because the loop is the point.
An interrupt-driven scope review captures crown jewels, threat actors, and analysis strategies. Three passes execute: structural hygiene, targeted attack paths, assumed breach. Readiness is counted, not judged — the dashboard narrates what the rules already computed.
Five stages from graph
to a report your board will read.
The Copilot moves through the same five stages every run, with you adjudicating the scope between stages two and three. Steps before scope are read-only; steps after are deterministic.
- 01
Read the topology
The Copilot opens by scouting your model — components, boundaries, data flows, classifications — and produces a structural overview. You see what it sees before any analysis is proposed.
- 02
Negotiate scope
An interrupt-driven scope review surfaces the analysis plan: crown jewels, threat actors, strategies. You confirm, edit, or reject before any agent runs. Scope is the contract; nothing executes until you sign it.
- 03
Run the analyses
Three deterministic passes execute against the graph: structural hygiene, targeted-path traversal, assumed-breach scenarios. Findings, attack scenarios, attack steps, and shadow components land back in the graph as first-class objects.
- 04
Score readiness
Readiness is counted, not judged. The math runs over graph conditions and produces severity tiles, evidence quality, trust badges, and per-crown-jewel coverage. Modeling debt and preventive coverage gaps surface as their own findings.
- 05
Export
Six formats, six audiences. Executive HTML for leadership, risk-committee HTML for the board, technical HTML and JSON for engineering, full-data JSON for archival, CSV for ticketing. Every export backed by the same audit trail.
Tour the workspace.
Every analysis lands in the same workspace — dashboard, findings, attack paths, and reports — anchored in the model graph. Navigate with the arrows, dots, or arrow keys.
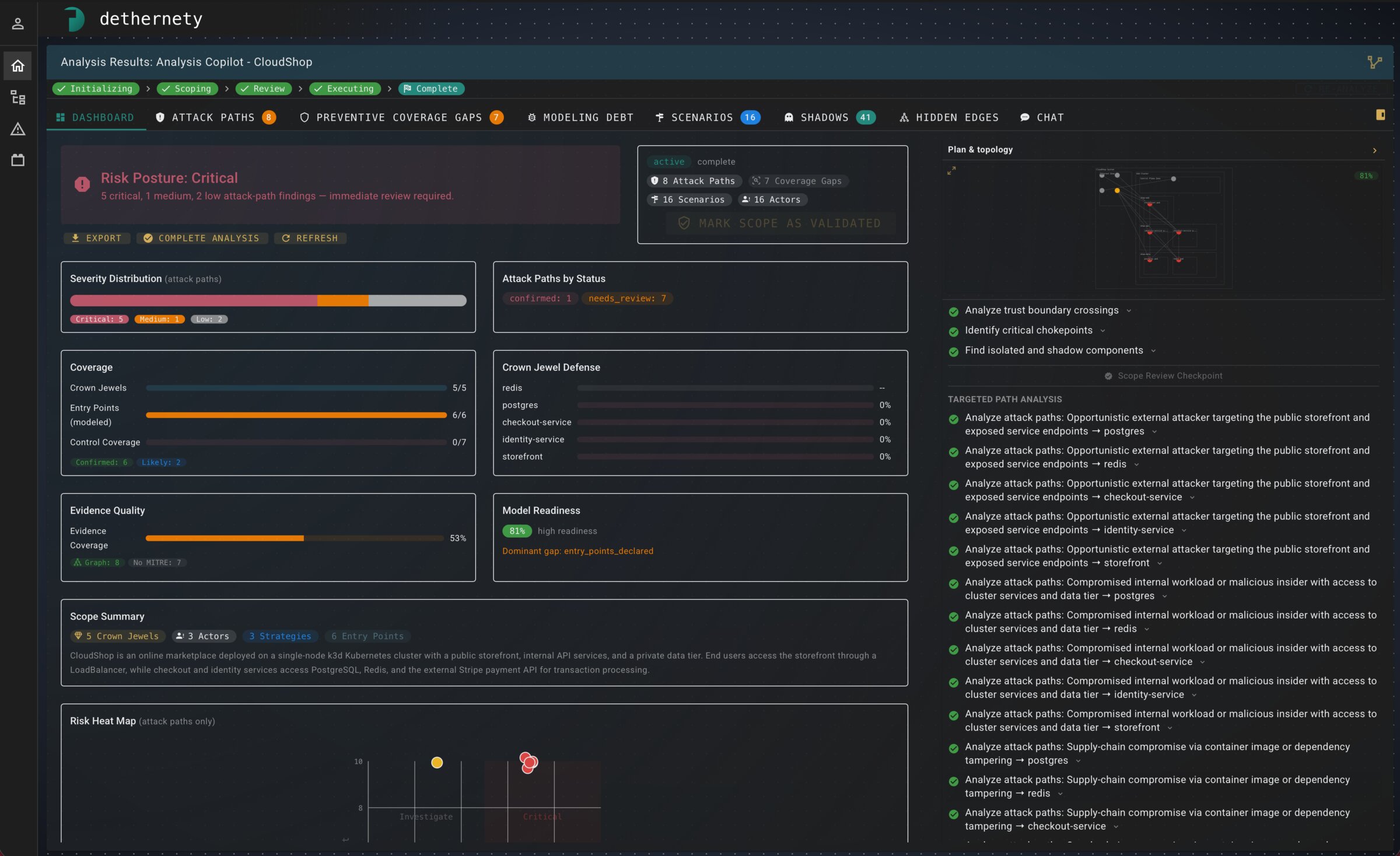
Dashboard
Risk posture, severity distribution, crown-jewel coverage, and model readiness — one workspace, every metric.
One model.
Six audiences.
The same analysis, packaged for whoever is reading. Same audit trail behind every export, so the leadership snapshot and the engineering technical doc tell the same story at different resolutions.
Risk posture, crown-jewel coverage, and headline gaps — formatted for a five-minute read.
Quantified risk, residual exposure, and the controls behind each readiness gate.
Findings, scenarios, evidence, and remediation guidance with full provenance.
Structured findings ready for ticketing, GRC pipelines, and downstream automation.
Complete graph snapshot — every node, edge, and attribute the analysis touched.
One row per finding with severity, owner, status, and remediation, ready to import.
Adjudicate the scope. Read the report.
The Copilot is hosted by Dethernety and integrates into the platform you already use. Sign in, pick a model, agree on scope, and the analysis runs.
Get Started